Internet Standards and Age Verification Architecture
A new IETF working draft sets out a technology-neutral framework for age assurance on the internet, comparing methods across service, device, and network enforcement layers.

This is a working Internet-Draft submitted to the Internet Engineering Task Force (IETF), the body responsible for developing the open standards that the internet runs on. Before a draft becomes a standard, it is published for review and comment by the wider technical and policy community. This draft is at that stage now.
It is authored by Mallory Knodel of the Social Web Foundation, Gianpaolo Angelo Scalone of Vodafone Group, Tom Newton of Qoria, and Audrey Hingle of Exchange Point, bringing together expertise across civil society, telecommunications, child safety technology, and internet infrastructure.
If you are working on age assurance policy, regulation, or implementation, this draft describes the technical landscape in terms that policy discussions can engage with directly. It sets out a solution-agnostic and technology-neutral framework for how various intermediaries can gate content and services based on age, analyses the effectiveness of each approach, and covers privacy, security and human rights considerations that any system will need to address.
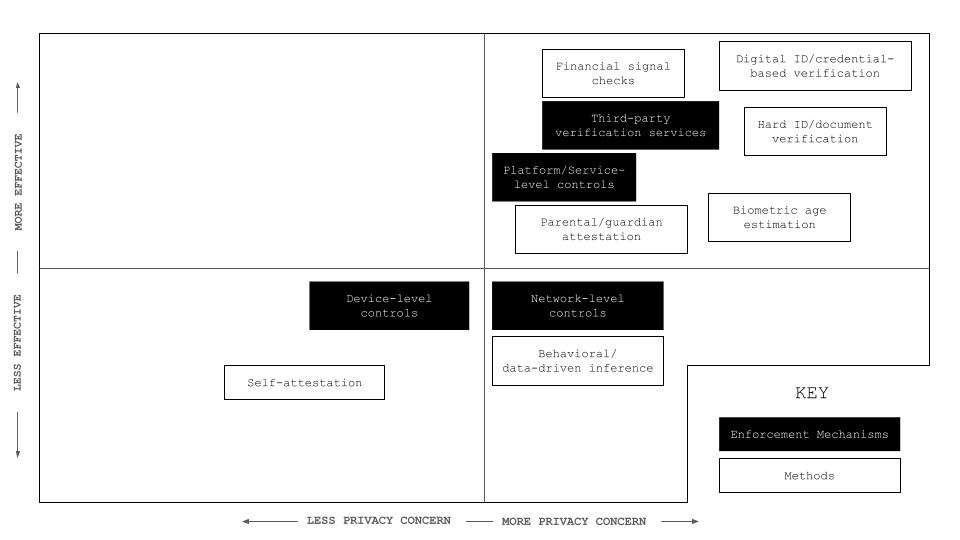
Many age verification methods conflict with data protection principles and pose serious safety, security, and privacy risks. Requiring all users on all platforms to submit verifiable credentials can create large, sensitive data stores in centralised intermediaries that are vulnerable to breaches, fraud, or misuse. Once compromised, this information is difficult if not impossible to secure again.
Reducing harm to children on the internet requires an incremental, all-hands approach and cannot be solved by age verification alone. A more resilient approach relies on a plurality of mechanisms operating at different layers of the internet architecture, each limited in scope and aligned with privacy-by-design principles.
Not all platforms are the same
Age-assurance mechanisms cannot be applied uniformly across the internet because different platforms have different relationships with their users, with personal data, and with the law.
Core internet infrastructure should remain neutral. Asking networks to make decisions about individual users introduces censorship risks. Government services, by contrast, are already identity-bound by law and can treat age as part of an existing verified identity framework. Essential services such as banking, healthcare, and education must stay broadly accessible, so the bar for age assurance here should be low.
General-use platforms are the most contested area. Social media, messaging, gaming, and app stores mix adult and minor audiences at scale across many jurisdictions. Each has its own enforcement logic: a messaging platform cannot inspect private content, so it relies on account or device-level signals; a gaming platform can use guardian consent and payment signals; an app store can enforce consistent age labels that flow through to the apps it distributes.
What counts as adult content also varies by jurisdiction. Material classified as restricted in one country may be considered normal commercial or artistic content in another. Any system has to account for this rather than impose a single global classification.
This Week's Links
Age Verification & Social Media Bans
- The EU's age verification app is technically ready, von der Leyen announced, telling online platforms they have "no more excuses" for not checking users' ages. The app lets people verify their age via passport, national ID, or trusted providers like banks, without platforms logging any personal data. https://www.politico.eu/article/eu-says-age-verification-app-is-technically-ready
- Roblox will need age verification to make sure you’re at least 9 years old. People who don’t do an age check can only access family-friendly games. https://www.theverge.com/games/910218/roblox-age-verification-check-games-kids-select-accounts
- Researchers from Harvard's Berkman Klein Center argue in Science that blanket social media bans and age restrictions for children are blunt, often counterproductive tools, and that evidence-based design approaches such as trust-building, help-seeking pathways, on-device nudges, and participatory education offer a more effective path to digital child safety. https://www.science.org/doi/10.1126/science.aec7804
Open Social Web
- What if social media was designed from the ground up to support local communities? That’s the question New_ Public had in mind when they built Roundabout: a local community platform with curated feeds, event calendars and more built on AT Protocol. Prosocial Design Network sat down with four members of their team, Sam Liebeskind, Trei Brundrett, Blaine Cook, and Adit Dhanushkodi, to learn more about it. https://www.prosocialdesign.org/blog/building-roundabout-a-pro-social-platform-for-local-communities
- Researchers from EPFL and Princeton introduce Bonsai, a tool that lets users create intentional, personalised social media feeds on Bluesky using natural language prompts rather than engagement-optimised algorithms. A two-week study found users felt more in control but building good feeds took more effort than they expected. https://arxiv.org/pdf/2509.10776



